The Lone Wolf Who Is He? The Sigma Male Personality Traits You Need To
May 16, 2022 · 14 min read The Case for SIGMA Rules Creating SIGMA Rules Recommended Background & Context Let's Create a Simple SIGMA Rule! An idea (and some thoughts on detection engineering with SIGMA) A data source / A log source Fitting the detection idea to SIGMA Logsource component Detection component Selection sub component (s):

Sigma Rules List PDF PDFfile
Sigma Rules are YAML-written textual signatures designed to identify suspicious activity potentially related to cyber threats anomalies in log events. One of the main advantages of these rules is their standardized format that permits writing the rule once and applying it across various SIEM products without needing to rewrite the rule.

15 Signs You’re An Alpha Male
Kaspersky actively involves SIGMA in its practice: the latest report on crimeware, " The common TTPs of modern ransomware groups ", includes over 70 SIGMA rules that simplify the work of security specialists. During this webinar, Kaspersky experts will provide a short overview of the SIGMA history, explain the main technical details - and.

Sigma Rule Attitude Whatsapp Status Video, Best Attitude HD Status Video
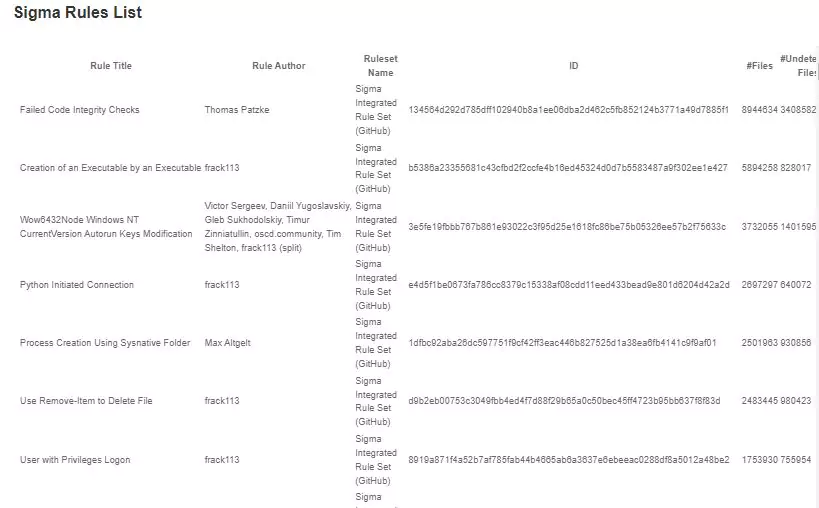
SOC Prime users are now armed with high-quality detection content to proactively defend against the most common adversary behaviors and tools applied by threat actors in destructive cyber-attacks. The Sigma Rules list called "Smoking Guns" is based on the recommendation engine that harnesses collective industry expertise and peer-driven.
Sigma rule easeroden
The Smoking Guns Sigma Rules list serves as a universal solution for a wide cybersecurity audience offering high-fidelity alerts to identify critical security gaps and providing an immense.
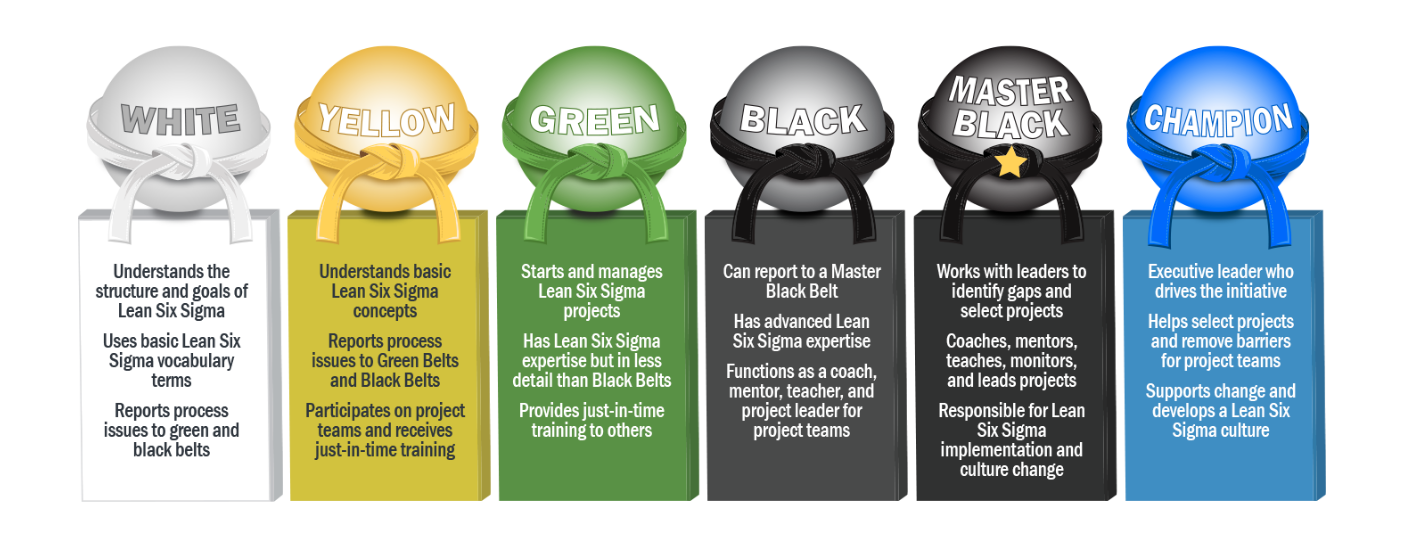
What Is Six Sigma?
Sigma Rules Examples 0xffccdd · Follow 3 min read · Dec 2, 2022 Sigma rules are a powerful tool for enhancing the capabilities of SIEM (Security Information and Event Management) systems.

Sigma Rule Memes And Meme Sound Download Memes.co.in
sigma master 24 branches 37 tags Code nasbench Merge PR #4659 from @nasbench - Reduce `Remote PowerShell Session (PS… 36290c5 4 days ago 15,992 commits .github chore: archive new rule references and update cache file ( #4652) last week deprecated Merge PR #4577 from @nasbench - Multiple Fixes & Updates 2 weeks ago documentation

What the HELK? SIGMA integration via Elastalert by Roberto Rodriguez
Sigma rules are textual signatures written in YAML that make it possible to detect anomalies in your environment by monitoring log events that can be signs of suspicious activity and cyber.

Alpha Male Characteristics, Alpha Male Traits, Male Mindset, Male Logo
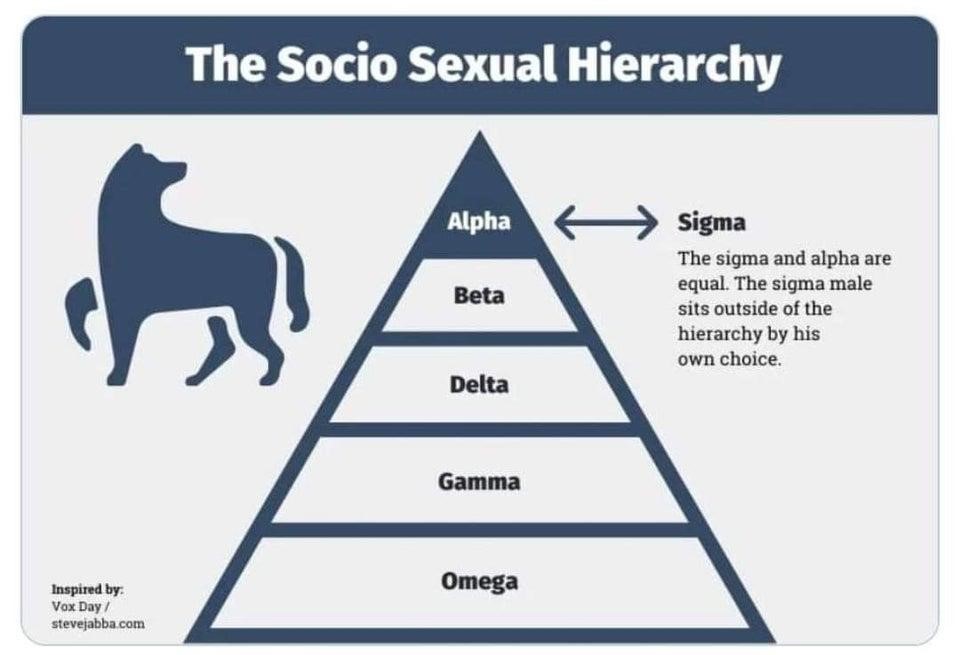
Gamma Male Omega Male Zeta Male But there is one type of male that lives outside the hierarchy. He's not subject to the alpha's dominance, nor does he want to compete with the betas - he is the Sigma Male. Sigma males have a set of characteristics that make them both high-value and immune from social pressures.

Sigma Male 20 Personality Traits to Identify Him in 2022 Sigma male
Threat Hunting Sigma rules can be used to hunt for threats: Use the rules to detect when a certain attack or threat targets your organization. Check if your organization was breached by applying Sigma rules to old logs (assuming your organization aggregates logs for at least a few months).

[PDF] Sigma Rules List PDF Download PDFfile
Luckily, Sigma rules (a use-case converted into the Sigma specification is called a rule) serve as a strict format for analysts to describe a particular use-case and convert it for whichever.
Sigma Rules List PDF Download 2023
What are Sigma Rules? Introduced in 2017 by detection engineer Florian Roth and open-source security tool developer Thomas Patzke, Sigma is a text-based, generic, open signature format that analysts can use to describe log events, making detections easier to write.
mexicoukraine Blog
Sigma rule for NotPetya Ransomware Activity detection was developed and shared with the community by Florian Roth and Tom Ueltschi. Simultaneously, the SOC Prime Team helped the victims of the NotPetya attack on-site and remotely using Sigma rules alongside its own SIEM-native content..

60+ best sigma male quotes and captions for your photos Tuko.co.ke
List of open source community Sigma rules that match the sysmon events recorded via execution of the file under scrutiny in a sandbox. Number of matching Sigma rules of all the different severities. Number of matching Sigma rules of this specific severity. Sigma rule name. Sigma rule description. View the Sigma rule.
[PDF] Sigma Rules List PDF Panot Book
Sigma Rules List; Sigma rules; Crowdsourced YARA Rules; Get Started; Searching; Sigma Rules List Powered by Zendesk.

8+ Sigma Omegaverse RohitEleanore
0x2 : General specifications of Sigma Rules. The sigma rule consists of the following sections, we will understand it with one of third party Sigma Rule, which has been downloaded from the.